TL;DR
KBA and KBV still have a place in legacy and lower-risk authentication flows, especially as backup checks. But when a KYC decision depends on stronger proof of identity, ID verification offers a much more reliable basis than question-based methods.
Knowledge-based authentication still has a role in fraud prevention and account security, but what does that role look like today? When does it still make sense, and when is it too weak for a KYC decision?
In this article, we break down what knowledge-based authentication is, how static and dynamic KBA work, where question-based checks still fit, and when ID verification becomes the stronger option if you need proof of document validity, proof of user presence, and a cleaner record for fraud and compliance review.
Subscribe to receive a bi-weekly blog digest from Regula
What is knowledge-based authentication?
Knowledge-based authentication (KBA) is an authentication method built on facts a person is expected to know. A user may answer security questions to gain access to an account, recover access, or pass a step-up check.
Knowledge-based authentication can work in two different ways, depending on whether the questions are fixed or generated from outside records.
Static KBA
With static KBA, the user answers pre-set security questions created in advance. Common examples include a first school, first car, first employer, or mother’s maiden name. The appeal of this method is that it is easy to deploy and familiar to users.
The problem is that many of these answers are no longer secret. Social media, public records, older databases, and breach data have made classic security questions much weaker than they once appeared on paper.
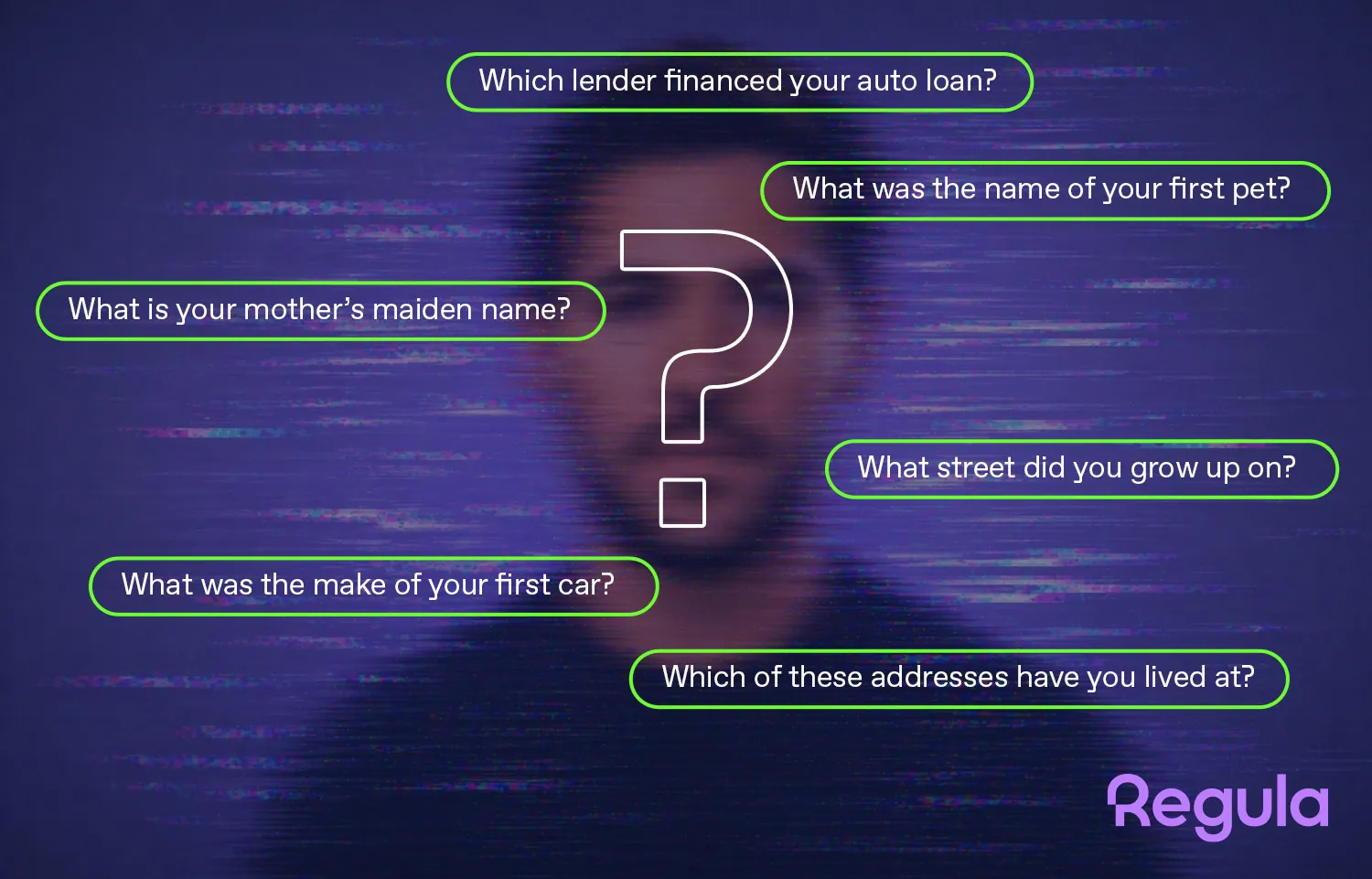
Dynamic KBA
Dynamic KBA does not use pre-set questions. Instead, it generates them in real time from third-party records. A user may be asked which street they lived on, which lender issued a loan, or which vehicle was never tied to their name. Compared with static KBA, this is the stronger version because the questions are built for that session and are not stored in advance.
A typical dynamic KBA flow looks like this:
-
The user provides personal information.
-
The system matches that data to outside records and generates questions.
-
The user answers within a limited time window and must meet a pass threshold.
-
The business either grants access or asks for another check.
Still, dynamic knowledge-based authentication has a built-in limit: it depends on outside records being deep, current, and accurate. That can create uneven results for thin-file users, younger applicants, recent movers, new arrivals, and people whose records are sparse or inconsistent.
That is why this process is useful only in a narrow set of cases, such as account recovery in older systems, step-up checks on existing accounts, and temporary bridge controls while a firm moves away from security questions.
Knowledge-based authentication vs. knowledge-based verification
The two terms are closely related, which is why they are often mixed together. The practical difference is where they appear in the verification flow.
-
Knowledge based authentication is usually used after an account already exists. Its job is to help confirm that the person trying to sign in, recover access, or pass a step-up check is the account holder.
-
Knowledge based verification (KBV) uses the same question-based logic, but during initial onboarding or proofing. Its job is to test whether an applicant knows enough about a claimed identity to pass a verification step.
As a result, KBV is highly situational and not a universally practical onboarding tool. In real use, KBV works only when a provider can match the applicant’s submitted information to enough outside records to generate usable questions.
For example, some companies in the U.S. can rely on SSN-linked records such as credit history, public records, or vehicle registration, and at least one major provider says users generally need about six months of credit history for the system to generate questions at all.
What are the pros and cons of knowledge-based authentication?
KBA still appears in some legacy flows because it is easy to add and familiar to users. However, the mechanism’s simplicity is also its main weakness: on its own, in current conditions, this check is rarely enough to stop identity fraud.
Pros
-
Easy to deploy. KBA does not require a camera, document capture, or biometric collection, so teams can keep older recovery and step-up flows running without a major system change.
-
Familiar to users. Many customers have seen security questions before, which means the check usually needs little explanation in older web and call-center flows.
-
Useful as a fallback. When stronger factors are not available, KBA can still add one extra hurdle instead of leaving the flow protected by a password alone. Still, it should not be mistaken for multi-factor authentication (MFA), because security questions and passwords both rely on knowledge.
Cons
-
It checks memory, not identity. A person can know or discover the answers without being the rightful account holder or the person in the session.
-
Static questions are easy to research. Common prompts such as a mother’s maiden name or first pet are often guessable or exposed through public and breached data.
-
Dynamic KBA can be unreliable in practice. It works only when a provider can match the user to enough outside records, which creates weaker coverage for thin-file users and people with limited credit history.
-
It leaves a weak audit trail. A passed quiz gives investigators and compliance teams much less to review than document checks, face matching, and liveness results.
-
Current guidance treats it very cautiously. NIST says KBA is no longer an acceptable authenticator for digital authentication, which is a strong warning against using it as the main control in higher-risk flows.
KBA can still help as a supporting control in older or lower-risk flows, but it is a poor choice for carrying the full identity decision on its own.
Knowledge-based authentication vs. ID verification
Given the balance of KBA’s strengths and weaknesses, many teams start looking at full ID verification as a more effective way to prevent identity fraud.
Does that mean ID verification is the better option in every case? Is there still a case for KBA today? Let’s break it down.
What ID verification does for your KYC
ID verification checks whether a person can present a valid identity document, whether that document passes authenticity checks, and whether the person in the session matches it.
A full ID verification flow, exemplified by Regula IDV Platform, includes the following steps:
-
Document capture. The user is guided to present an ID so the system gets usable images for analysis.
-
Document liveness. The platform checks that a physical document is in front of the camera rather than a screen, printout, or replay.
-
Document recognition and data extraction. The document verification technology identifies the document type and reads the data from the visual zone, MRZ, barcode, and, where present, the chip.
-
Authenticity checks. The platform validates security features and cross-checks fields from different data sources inside the document.
-
Face match and liveness. With biometric authentication software, a selfie or short video can be compared with the portrait on the ID, while liveness checks test whether the user is a live person rather than a spoof.
-
Decision and case handling. The result can go to automatic approval, manual review, added KYC checks such as sanctions screening, or stronger step-up controls triggered by risk signals such as geo/IP and device history.
A passed KBA check tells you that the user knew (or guessed) the right answers. It does not tell you whether the person in front of the screen is holding a genuine document, whether the document belongs to them, or whether the session is live rather than replayed.
ID verification, on the other hand, does. That’s why it is usually the much stronger control for onboarding and other higher-risk decisions.
KBA vs. ID verification: side-by-side comparison
The core features of KBA and ID verification can be summarized as follows:
|
|
KBA |
ID Verification |
|---|---|---|
|
What is being tested? |
Whether the user knows personal facts or account-linked answers |
Whether the user has a valid ID and matches it |
|
Main inputs |
Security questions or record-based questions |
Identity document, personal data, selfie or video, and liveness checks |
|
Can it prove live presence? |
No |
Yes |
|
Audit value |
Limited, usually a pass/fail result |
Stronger, with document images, personal data, match results, and liveness results |
|
Geographic reach |
Often tied to local data coverage and record depth |
Broader when the vendor supports many document types and countries |
|
Best fit |
Legacy account access, password recovery, step-up checks |
Onboarding, higher-risk actions, authorization, and stronger proofing |
For a KYC team, the practical difference between KBA and ID verification usually comes down to three questions:
-
Do we need proof of possession? If yes, KBA is weak because it does not prove the user has a document at all.
-
Do we need proof of presence? If yes, KBA falls short because it cannot prove that a live person is in the session.
-
Do we need reviewable evidence? If yes, ID verification tools such as Regula IDV Platform can give fraud teams, compliance staff, and reviewers a much stronger record.
Choosing ID verification over KBA
In the KBA vs. ID verification debate, it comes down to whether question-based methods should carry the main burden of proof in onboarding. In most higher-risk flows, the answer is no.
If a business needs stronger evidence, better audit records, and a clearer link between the applicant and the claimed identity, ID verification is the better choice. Question-based checks may still have a supporting role, but the main gate should be built on document authenticity, biometric comparison, and liveness.
This is why a solution such as Regula IDV Platform can be effective against newer forms of fraud: it covers end-to-end identity lifecycle management, combines document, face, and age verification in one system, keeps identity data in user profiles with full history, and gives teams role-based access, audit visibility, and a choice of on-premises, cloud, or hybrid deployment.