According to the Federal Trade Commission’s (FTC) report for 2024, US consumers had lost more than $12.5 billion to online identity fraud, much of which relies on identity signals that are easy to fake, borrow, or steal. And although this report is customer-focused, the mechanics map directly to what both B2C and B2B teams tackle on a daily basis: account creation, payouts, refunds, disputes, and recovery.
In this glossary-style guide, we will walk you through five common types of identity fraud that recur in online systems, with a reported case for each one, plus practical identity verification tips that should help you reduce repeat losses.
Subscribe to receive a bi-weekly blog digest from Regula
Account takeover
Account takeover occurs when an unauthorized individual gains access to a legitimate user account and uses it for theft or abuse. Credential stuffing is a common technique: attackers test large lists of leaked username and password pairs against a login page and wait for matches. Password reuse keeps this profitable, and automation keeps it cheap.
A real-world example
23andMe announced that, throughout most of 2023, attackers used credential stuffing to take over a fraction of customer accounts and then obtained additional data through its DNA Relatives feature, which links users with relatives.
TechCrunch reported that the incident affected 6.9 million users in total through that secondary access path.
The long-term consequences were not limited to public scrutiny, as some countries have since fined 23andMe for user privacy violations.

In fact, the fallout continued well after the initial breach news cycle: in June 2025, the UK Information Commissioner’s Office fined 23andMe £2.31 million for failing to implement appropriate security measures to protect UK users’ data.
Why account takeover is a problem
A correct password can be deceiving. Unless you weigh device, location, and session behavior, a stolen credential can pass as normal and slip into high-value actions before anyone notices.
Attackers often wait for the right moment. Many takeovers stay quiet until a payout detail is changed, a stored value balance is drained, or a data export is triggered.
B2B blast radius can be immediate. One compromised login can expose invoices, billing changes, and employee contacts that then support payment redirection and targeted phishing.
What can help
Make password-only logins less valuable. Strong MFA helps, and phishing-resistant options like passkeys or security keys reduce the usefulness of stolen credentials.
Treat “account control changes” as high-risk. Email changes, phone changes, payout edits, new device enrollment, and recovery attempts should trigger step-up checks and tighter limits.
Reinforce account recovery. If recovery is easy to hijack, takeover becomes a customer support problem instead of a security problem.
Add short holds after sensitive events. After a reset, new device, or payout change, delay withdrawals or transfers unless the user passes stronger verification.
SIM swap fraud
SIM swap fraud is a phone-number takeover: a criminal persuades a mobile carrier to transfer a victim’s number to a SIM controlled by the attacker, or to port it to a different carrier. Once that happens, one-time SMS passcodes and phone-based recovery flows can be intercepted, which turns a phone number into a key for email and financial accounts.
A real-world example
The hacking of the SEC’s @SECGov X account back in 2024 shows how SIM swaps can compromise even major accounts.
In a Justice Department release, prosecutors said conspirators executed a SIM swap of the phone account associated with the SEC’s X account in January 2024 to gain unauthorized access and publish a fraudulent post about Bitcoin ETFs.

The post has caused a significant stir amongst crypto enthusiasts.
According to the official statement, the defendant obtained a replacement SIM by presenting false information at an AT&T store, then bought a phone at a nearby Apple store to receive the verification code and pass access to co-conspirators.
Why SIM swap fraud is a problem
It undermines SMS-based login and recovery. If your product trusts phone possession for resets, a SIM swap can turn into account takeover quickly.
Your security depends on another company’s counter staff. A carrier store or call center decision can effectively bypass your own controls, even if your internal security is strong.
It combines easily with other tactics. Stolen personal data, phishing, and support manipulation often show up in the same incident chain.
What can help
Use stronger factors for high-stakes actions. Keep SMS codes for convenience where needed, but require stronger authentication for recovery, payout edits, and large transfers.
Treat phone number changes and new SIM signals as high-risk. Add step-up checks and temporary restrictions when a number changes or a new device appears.
Offer phishing-resistant sign-in options. Passkeys and authenticator apps reduce reliance on phone-number control.
Require recovery proof that survives phone takeover. For risky recoveries, ask for verification that ties the claimant to an existing identity record, not just to a phone number.
Bonus abuse
Bonus abuse is the repeated collection of sign-up incentives, referral credits, deposit matches, free trials, or “new customer” perks by someone who is not actually a new customer.

Despite many conditions required to redeem bonuses (as seen at the bottom), fraudsters are still often successful at abusing them.
The most common way of performing this is multi-accounting: one person creates many accounts under different identity details, then redeems the same offer again and again.
A real-world example
In February 2026, the US Attorney’s Office for the District of Connecticut announced a 45-count indictment alleging that two men used the personal information of about 3,000 identity theft victims to open accounts on FanDuel and other online gambling services, take advantage of promotional bonuses and credits, and route proceeds through stored value cards and financial accounts they controlled.
Prosecutors alleged roughly 3,000 victims and about $3 million in profits tied to the scheme.
Why bonus abuse is a problem
Losses hide in small payouts. Thousands of low-dollar redemptions can outperform a single big theft because they blend into normal activity.
Referral systems get weaponized. When referrals have cash value, fraudsters recruit helpers and rotate identities to harvest rewards repeatedly.
Regulated sectors face extra exposure. Gaming, wagering, and fintech often have “one account per person” rules and monitoring requirements, so the identity failure becomes a compliance issue too.
What can help
Tie promo value to proof of personhood at cash-out. Many platforms keep signup light, then require stronger identity proof before the first withdrawal or higher-value redemption.
Add “one human, one account” controls that are hard to fake. Device fingerprinting, phone reputation, and behavioral signals help, but strong ID checks plus selfie match are often the decisive barrier when money leaves the system.
Defend the referral loop. Require identity verification before referral rewards become withdrawable, and delay high-value rewards until the referrer and referee show normal use.
Make withdrawal changes high-friction. If a user changes payout destination, treat that like a risk event and apply stronger checks.
Refund fraud
Refund fraud is the manipulation of return and refund workflows to get money back while keeping the product, receiving a replacement that was never justified, or getting a refund on a transaction that was not eligible.
In physical goods it can look like false “item not received” claims, “empty box” returns, or damage reports backed by mismatched photos. In digital services it often appears as “I didn’t authorize this” tickets filed after the service has already been used.
A real-world example
In December 2025, the Minnesota Star Tribune reported that major retailers were losing millions to online refund fraud rings and highlighted the “Noir Luxury Refunds” operation, which prosecutors said was run from Egypt and had US-based participants, with a Minnesota man expected to plead guilty.
A related DOJ release from April 2025 describes how that operation worked in practice: customers paid a percentage fee, and the group then used social engineering to pressure customer service into issuing refunds. On top of that, they manipulated shipping labels so a retailer believed a return was received (when it was not), recruited customer service insiders, and even developed malware intended to bypass retailer defenses.
Why refund fraud is a problem
It targets your customer-facing teams. Customer support and returns are optimized for speed and goodwill, which fraudsters exploit with scripts and persistence.
It scales well. Once a ring has a working playbook for a retailer, it can be reused with minor edits and sold as a service.
It creates internal tension. Fraud controls that feel punitive can harm legitimate customers, so teams sometimes hesitate to add friction even when losses are obvious.
What can help
Treat refund payouts as identity checkpoints. Recheck identity on high-value refunds, repeat claimants, and destination changes.
Use step-up verification for exceptions. Off-policy refunds, replacements without return, or unusual claim patterns should require stronger proof before approval.
Instrument the support channel. Look for repeat scripts, rapid escalation patterns, account access from new devices, and identity inconsistencies that do not fit the account history.
Tighten return logistics signals. Validate carrier events, detect label reuse, and flag tracking patterns that suggest label manipulation.
Chargeback fraud
Chargeback fraud, often called friendly fraud, is the misuse of card dispute rules to reverse a legitimate purchase. Sometimes the buyer is acting in bad faith, and sometimes confusion triggers it after a subscription renews or a billing descriptor looks unfamiliar.
Either way, the merchant can lose the sale, the product, and a dispute fee.
A real-world example
Australian ABC News reported in late 2025 that small business owners were losing thousands to chargebacks filed by online shoppers disputing legitimate transactions and claiming refunds, even when merchants provided evidence that goods were ordered and delivered.
For example, one entrepreneur told the media she sold two baby bags, had proof of delivery, and still lost the sale after the buyer filed a chargeback. She said she later found the same bags listed for resale on Facebook by the same buyer, turning a routine online order into a double loss plus a fee charged during the dispute process.
Why chargeback fraud is a problem
The dispute process can favor the cardholder. Merchants can submit evidence and still lose, especially when the claim is framed as unauthorized.
The operational burden is real. Each dispute requires staff time, documentation, and deadlines, even when the merchant believes the claim is false.
High dispute ratios create second-order damage. Payment providers may impose monitoring, reserves, or higher processing risk when dispute rates rise.
What can help
Prevent disputes before they can happen. Use recognizable billing descriptors, send renewal and trial-end notices, and make cancellation easy to find.
Use step-up checks on risky orders. High-value items, unusual shipping patterns, and first-time buyers are common triggers for added verification before fulfillment.
Keep evidence that ties the buyer to the purchase. Identity verification events, device history, delivery confirmation, and customer communications help when a dispute is filed.
Use early dispute alerts where available. When you can refund before a dispute turns into a chargeback, you can cut fees and reduce ratio impact.
How Regula prevents online identity fraud in its many forms
The above identity fraud types follow roughly the same playbook: find the moment where identity is accepted with minimal proof, then repeat the exploit at volume. Interestingly, the countermeasures overlap as well: step-up checks at login recovery, payout and withdrawal gates, refund exceptions, higher-risk purchases, and good record keeping.
All of these countermeasures can be provided by Regula IDV Platform, built for robust identity verification (during signup) and orchestration (over the whole customer lifecycle).
Regula IDV Platform will help you prevent online identity fraud with:
Workflow-driven step-up verification for onboarding, recovery, and high-risk actions (e.g., payout destination changes, first withdrawals, refund exceptions).
Complete document and biometric verification, backed by the biggest template database in the world (16,000 from 254 countries and territories).
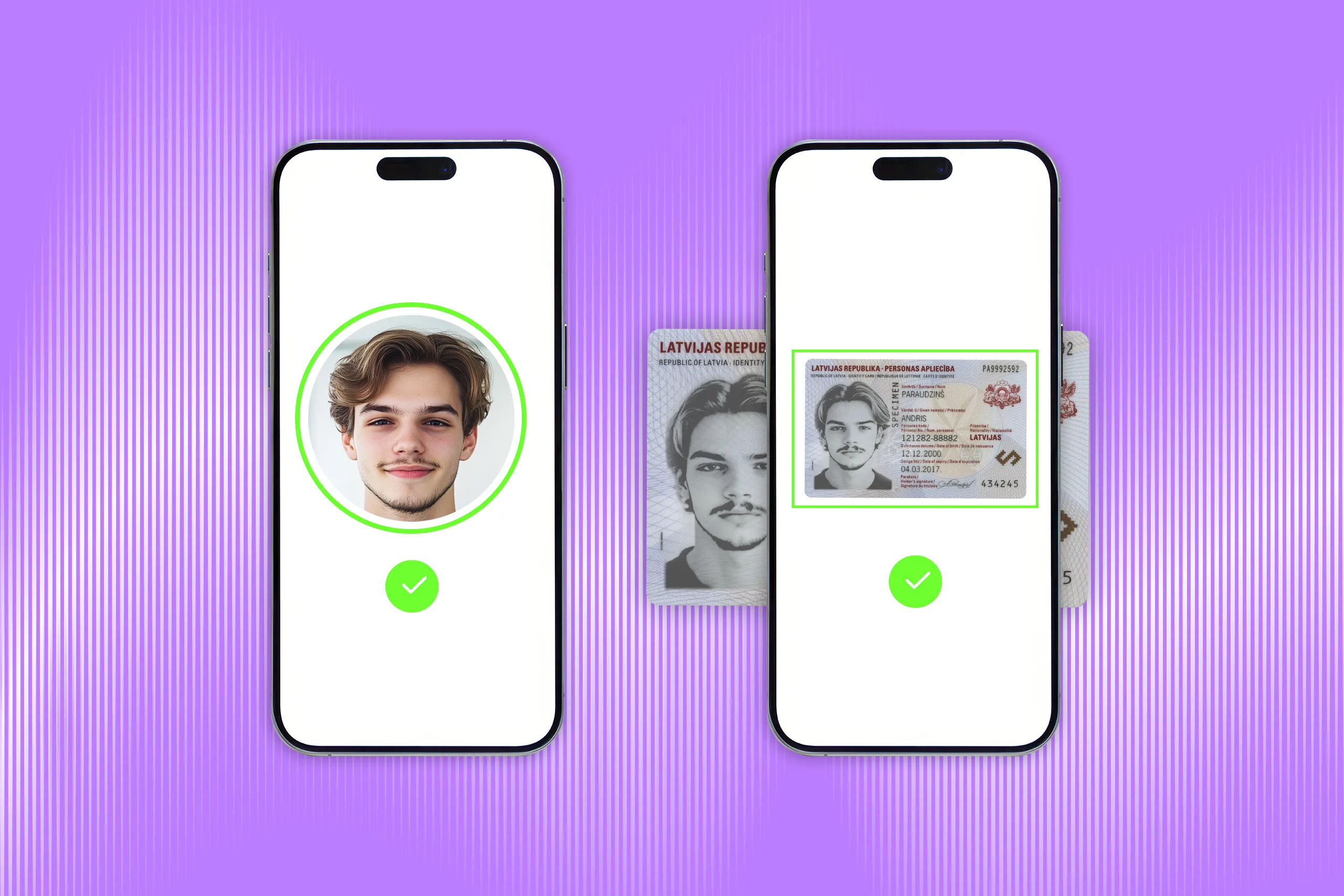
Instant facial recognition with liveness detection, preventing the use of static face images, printed photos, video replays, video injections, or masks.
AML/PEP screening, as well as validation against trusted global databases.
Session and user management with analytics via the Platform portal, which supports full control over every user’s identity and reduces complexity with a single user authentication flow covering all your verification needs.
Broad integration options (mobile and web) with your existing tech stack and third-party systems through customizable connectors.
Regulatory compliance: Effortlessly adhere to regulations across multiple jurisdictions with robust, built-in compliance capabilities.





.webp)