Today, most companies have moved from perimeter-based, on-premises environments to hybrid and cloud-first access models where employees, partners, and customers all access systems remotely.
The data confirms this shift.
Despite post-pandemic “back-to-the-office” campaigns, many employers still rely on remote work as a regular practice. As of April 2025, more than one in five US workers — almost 35 million people in total — worked from home at least part of the time.
At the same time, more businesses are selling products and services online. For example, in 2025, global retail e-commerce sales alone exceeded $3.6 trillion.
This transition has turned identity into a board-level risk, as security incidents, regulatory pressure, and rising customer expectations are forcing organizations to rethink how they manage access.
Yet many companies still treat identity proofing as separate from identity and access management (IAM). As a result, access decisions are often based on credentials and roles — even when the organization has limited assurance about who is actually behind those credentials.
In this article, we explain the core IAM concepts and components, and show how they intersect with — and can be enhanced by — modern identity verification.
What is identity and access management (IAM)?
Identity and access management ensures that, within an IT system, the right users get the right access to the right resources at the right time, while bad actors are denied entry.
In this context, resources vary from emails and databases to apps and internal data, and users include employees, contractors, partners, and customers. IAM policies can be enforced across both corporate and personal devices (computers, laptops, and smartphones), becoming a control level in a scattered network of tools and users.
In practice, a robust identity and access management strategy supports not only security but also company growth, as more operations behind the scenes are automated. This contributes to faster onboarding, remote workforce scaling, and a reduced help desk load. As a result, organizations can quickly and accurately authenticate users and grant role-based access without delays — even across locations and jurisdictions.
Subscribe to receive a bi-weekly blog digest from Regula
The core components of an identity-first IAM system
At a high level, IAM consists of two main parts:
Identity management covers how identities are created, maintained, and governed over time. It includes user profiles, attributes, lifecycle events, and access entitlements. One of the key functions is validating login attempts against an identity database and maintaining records of everyone who should have access, such as names, job titles, phone numbers, and email addresses. This information is constantly updated as employees join or leave an organization, and as clients onboard or offboard. Roles, permissions, and risk levels may also change over time, and identity management must reflect those changes.
Access management monitors which resources a person has permission to access. Most companies use different levels of access determined by factors such as employee job title, customer risk level, location, and other attributes. Like login information, access rights can evolve in accordance with changes in users’ activities, transactions, or roles.
These components define an identity and access management strategy at a very basic level. In real environments, modern IAM can form a complex, multi-layered infrastructure, with many processes and policies working together. When identity is placed at the center, such a system becomes both a security foundation and a business enabler, integrating contexts and ensuring consistency across all underlying procedures.
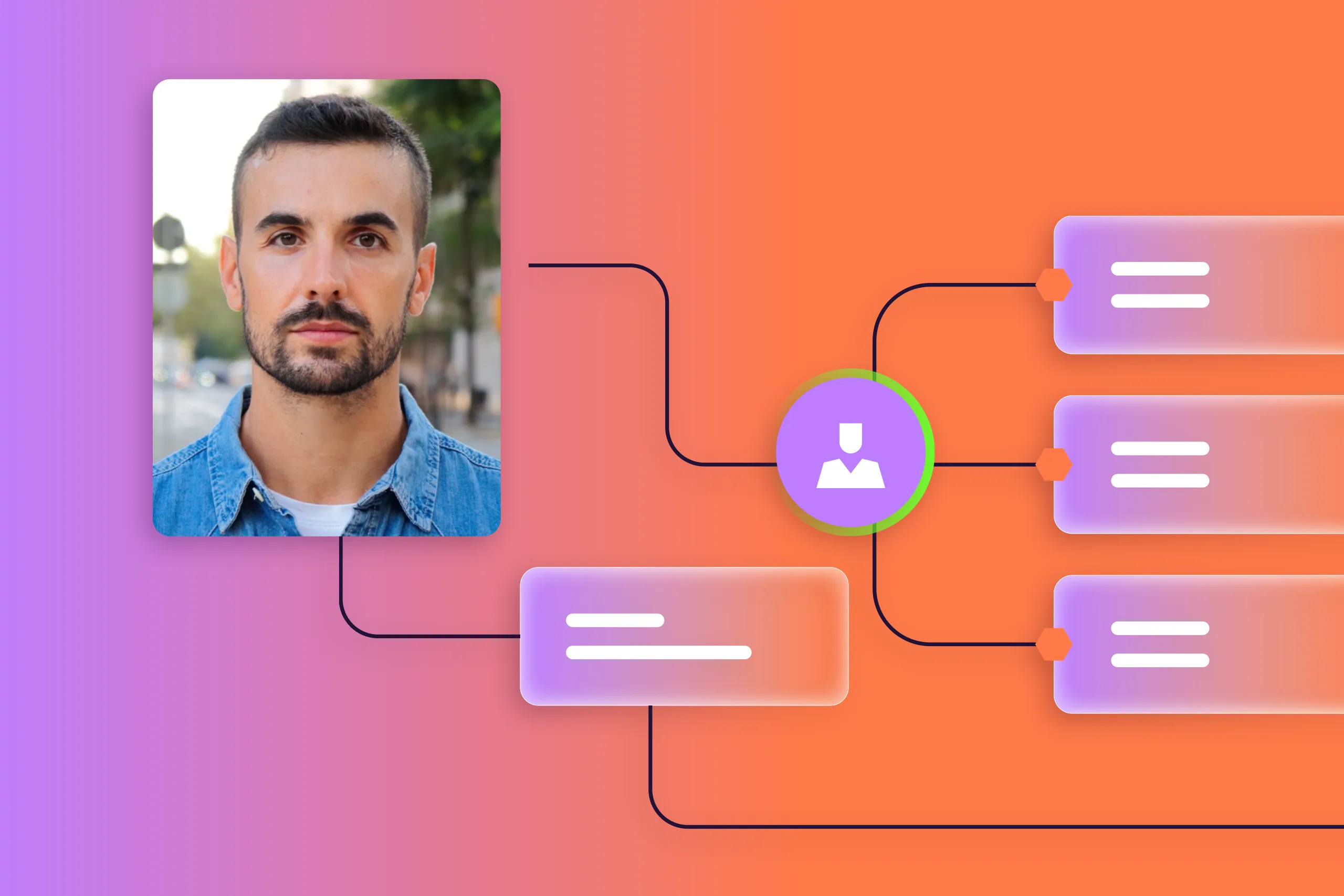
The diagram below illustrates this complexity.

Identity-first IAM goes beyond access-related procedures, establishing both security and digital trust in a zero-trust world.
Let’s take a closer look at the smaller parts of identity and access management systems.
Access management and authentication
One of the core components of the IAM framework is user authentication. It verifies that a person is who they claim to be when accessing digital systems. For this reason, authentication is always preceded by identity enrollment in the system when an identity record is created for the first time.
The identity enrollment flow differs depending on the IAM use case. For example, workforce IAM typically involves pre-registration of new employees and providing them with ready-made credentials. In many businesses, enrollment (or registration) is left to customers, who can create their own credentials, which the company can approve or deny based on security requirements.
Credentials, also called authentication factors, range from simple to advanced. Examples include passwords, one-time or permanent verification codes, and biometrics like fingerprints or facial scans.
Authentication methods vary based on:
The number of factors used (single- or multi-factor).
The type of factor used (password-, biometric-, or token-based).
These processes are intersected with authorization maintaining secure and smooth access to the system for different user groups based on their access level. In particular, authorization defines what users are allowed to access once authenticated.
Typically, authorization is built on access levels — specific permissions within a system that determine what data users can view, edit, or manage based on their role. A common hierarchy (from the highest to lowest) is:
Administrator
Editor
User
Guest
In addition to regular authorization, the IAM framework includes access revocation — removing or disabling a user's rights to systems or data. This usually occurs when an employee leaves the company or a user deletes their account.
Customer identity and access management (CIAM)
Customer IAM is a part of IAM that supports the management, authentication, and authorization of clients and other users outside the organization.
Typically, CIAM relies on self-service capabilities, meaning users register in the system themselves, while most underlying processes (including authentication and authorization) must be secure and automated to keep the experience customer-centric and seamless.
For instance, high-risk actions typically require step-up authentication using phishing-resistant MFA (for example, passkeys or device-bound authenticators), along with contextual signals such as device, location, network, and behavioral risk indicators.
Identity verification
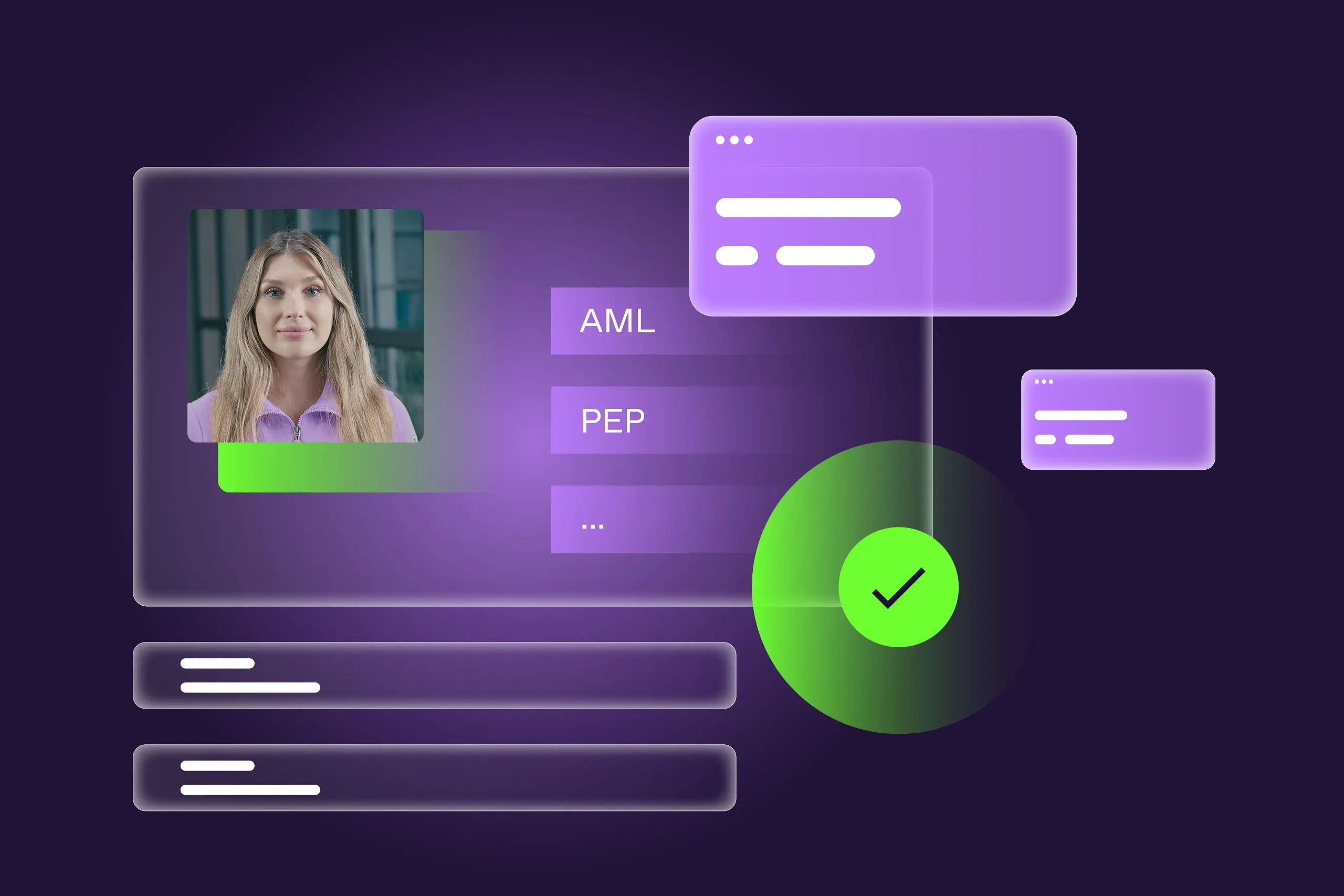
In some cases, registration requires more than signing up with an email and password, but also confirming that the declared identity is real. This procedure is called identity verification (IDV) and involves submitting official documents like a government-issued ID and/or biometric data (often a selfie). IDV is further strengthened by KYC policies, where a verified user is additionally checked against third-party sources such as watchlists and PEP databases.
In the IAM context, identity verification provides assurance that:
During registration, the user exists in the real world.
During authentication, the user is the true account owner.
During authorization, the user is eligible to access specific resources/features in accordance with their risk level.
IDV is closely connected to re-verification, when a customer’s identity must be confirmed again due to specific conditions. For instance, the submitted ID may have expired, suspicious activity may be flagged under the user’s account, or user data may have been compromised in a security incident.
Re-verification may rely on a one-time password (OTP) or email confirmation code. It does not always require completing a full IDV procedure.
Privileged access management (PAM)
Earlier, we explained the level-based nature of access management, where the highest roles are administrative. Administrators typically manage and protect accounts, configure permissions and credentials, and control the use of apps and databases across the entire system. In simple terms, they enable and oversee technical access to IAM controls. The policies and tools that govern this level of access fall under privileged access management (PAM).
Typically, PAM includes five subflows: privileged account and session management, privilege elevation and delegation management, secrets management, remote PAM, and cloud infrastructure entitlement management. This classification shows that PAM goes beyond managing human identities. It also defines privileged access for machines, apps, and systems.
PAM includes authentication and authorization procedures, but authentication requirements at this level are typically stricter. While users with regular access permissions may rely on basic methods like passwords, administrators usually require MFA, including biometrics, OTPs, or hardware tokens.
Identity governance and administration
IAM also includes an identity governance layer that helps administrators manage regulatory compliance related to digital identities and access rights, controlling who has access to what resources, for what reason, and for how long.
Identity governance may appear to be synonymous with IAM, but it’s not. While IAM focuses on ensuring secure access for the right users, identity governance emphasizes oversight and control of IAM tools and policies from a compliance perspective.
Typical identity governance tasks include periodic access reviews, audit reporting, and compliance documentation. For instance, many organizations must comply with regulations such as GDPR, HIPAA, and the SOX Act.
Identity lifecycle management
Finally, one more element completes the IAM picture: identity lifecycle management. This process spans all the previously mentioned components and includes three main stages that every user passes through:
Onboarding: Registration, account provisioning, initial access assignment, and identity verification.
Ongoing monitoring: Authentication, authorization, access updates, and re-verification when needed.
Offboarding: Access revocation and data deletion when users leave the organization or stop being customers.
Now that we have a clearer understanding of IAM, let’s explore how this approach can be strengthened through IDV.
Where identity verification fits into IAM tools
Before diving deeper, it’s important to clarify the key difference between identity verification and authentication. Both approaches inform the system about a particular user’s identity, but in practice, IDV reveals “who the user is,” while authentication only confirms that the credentials match the stored identity record.
Why is it critical?
Example: A user registers in the system with an email and password. Their account record is created in the database. When they log in next time, their credentials are matched against the database entry. If successful, the user is authenticated and can enter the system.
However, these credentials can be used by anyone (due to data sharing or — even worse — a data breach). In this case, from the IAM system’s perspective, the user remains the same, while in reality, it may be another, unauthorized person.

While IDV reveals the user’s real-world identity, authentication only checks which credentials are being used.
The key difference is that IDV verifies a real user’s identity by relying on government-issued IDs, national identity databases, and/or biometrics (face captures, fingerprints, or voice). In contrast, authentication, as part of an IAM toolkit, verifies the user’s digital identity by relying on authentication factors. If these factors are depersonalized, such as passwords or tokens, the system doesn’t always know who is actually logging in.
This gap creates an opportunity for fraudsters who use stolen credentials for account takeovers and obtain unauthorized access.
Moreover, bad actors may use identity theft methods to create fraudulent identities from scratch by registering as legitimate users using stolen or fabricated personal information. Today, this often involves synthetic identities — a mix of real and artificial data representing a person who doesn’t exist.
When added to the user journey as an extra layer of control, IDV significantly reduces the risk of such incidents.
Common scenarios where IDV is critical include:
Customer onboarding and account creation
From an IAM perspective, registration and onboarding can be supervised by administrators. However, many digital companies — from banks to marketplaces — allow customers to onboard themselves, meaning users generate credentials and activate accounts independently.
With IDV in place, this process becomes more secure and reliable, as the company verifies the real-world identity of the individual entering the system, not just their digital credentials.
Real-world example: Venmo, a payment service, notifies customers that it must collect personal information from users who maintain a balance. The company applies different verification scenarios depending on the case. For example, to verify their name or date of birth, a customer may submit a passport, driver’s license, DHS card, proof of address, or complete Social Security Number verification.
Remote employee access
Distributed teams are now a standard operating model. While customers may fall into lower access tiers, remote employees, particularly those in senior or technical roles, often require elevated permissions.
In this case, employee identity verification can serve as an additional security layer before a remote worker is granted long-term access to internal systems and databases.
Real-world example: Some organizations use IDV tools in remote employee attendance systems. For instance, selfie-based facial matching with liveness detection and document verification may be incorporated into login or clock-in procedures.
Partner and contractor access
Organizations that work with a number of third-party contractors face elevated insider risks, especially when these individuals access sensitive data. Using IDV tools to verify partners, contractors, and advisors is a strong risk mitigation practice.
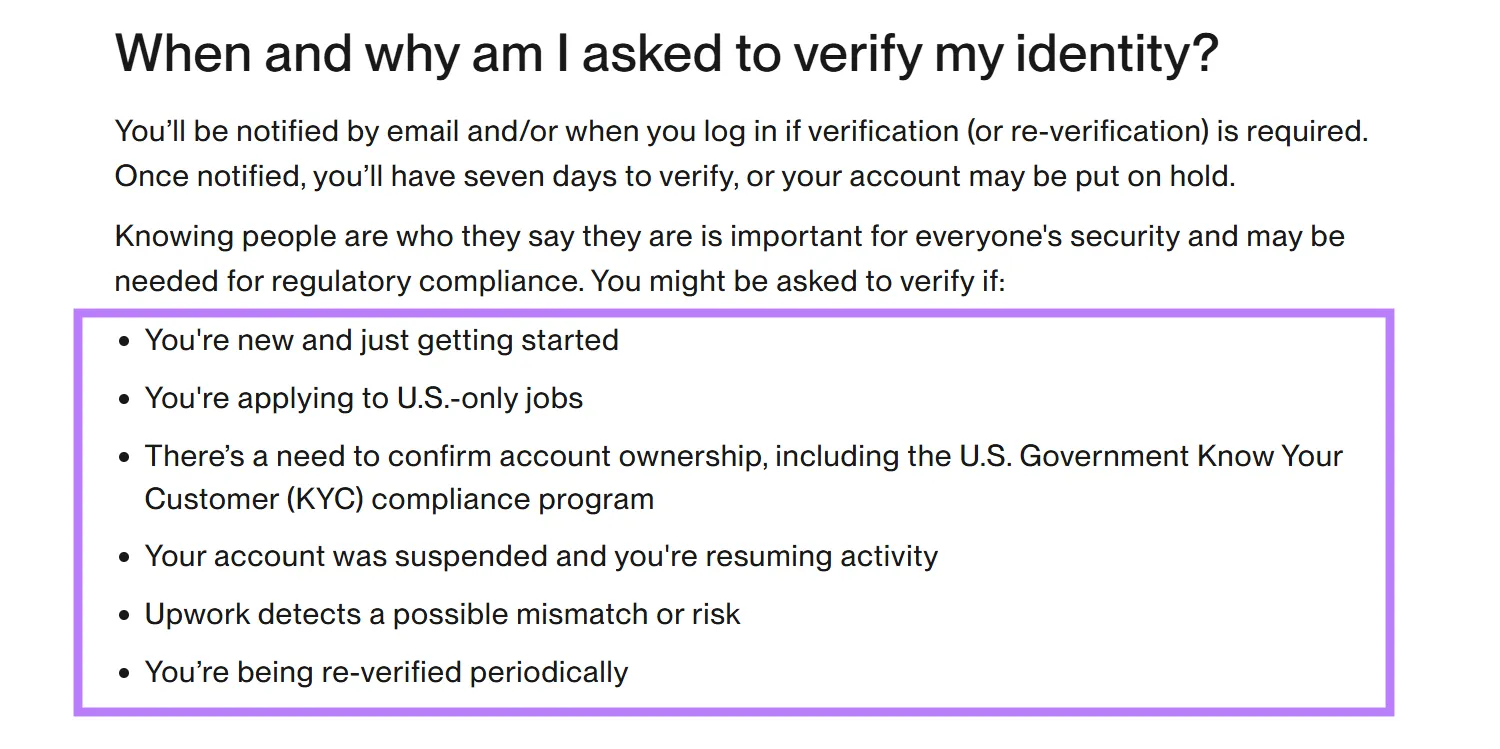
Real-world example: IDV is often used by intermediaries such as freelance platforms. Upwork may request identity verification during account creation, when suspicious activity is detected, or when users search for jobs in certain locations.
Regulated industries and KYC/AML requirements
In many jurisdictions, IDV is mandatory for organizations in banking, fintech, telecom, gambling, and increasingly social media platforms.
Depending on local regulations, companies must incorporate identity checks, often involving document verification, biometric matching, and age verification, into processes such as onboarding, opening bank accounts, or applying for loans. From an IAM perspective, this means collecting and managing more verified identity data alongside authentication credentials.
Real-world example: Traditionally, financial institutions have been major IDV adopters due to regulatory requirements. However, newer sectors are now affected.
For example, Discord announced that it will roll out teen safety features globally in the second half of 2026. Users who want to modify certain settings or access sensitive content must verify their age through ID submission or facial age estimation.
The business value of IDV platforms within IAM
IAM administrators and risk managers are now dealing with more complex IT systems than ever before. These systems contain a growing number of digital identities with different access levels, often requiring different security approaches and policies. As systems expand across organizations, it’s becoming increasingly difficult to manage all IAM tools and processes effectively.
In high-assurance scenarios, including onboarding, account recovery, or high-risk actions, organizations often incorporate IDV. But how can this be done smoothly for users and efficiently for administrators?
Integrating third-party services for document, biometric, or age checks is common practice in many companies. However, the larger the IAM system becomes, the more challenging integration is from both an architectural and maintenance perspective. Adding IDV tools as “patches” creates additional flows and intersections in the customer journey, increasing friction.
This fragmentation also increases integration costs, slows deployment cycles, and creates ongoing maintenance overhead for IT teams.
For this reason, enterprises are increasingly adopting IDV platforms rather than standalone IDV solutions. The key difference lies in the approach. While individual IDV tools typically address one or two verification tasks, such as document or biometric matching, platforms orchestrate a complete IDV process that may include multiple steps: document authentication, biometric verification, liveness detection, data validation, and KYC/AML screening.

Like an IAM system, an IDV platform acts as a control center where administrators configure and manage multiple verification tools within a single secure and auditable workflow.
IDV platforms also bring another important advantage: they manage the entire identity lifecycle, enabling workflow orchestration and allowing administrators to tailor verification procedures for each user through automation. That means every client’s location, job role, age, or specific transaction can automatically determine the verification path they follow during onboarding or KYC checks.
IDV platforms also simplify control over authentication and access-related procedures, as well as broader identity lifecycle management. Risk managers can adjust verification flows without rebuilding apps. This is particularly valuable for repeat checks, such as reverification after high-risk changes, new device logins, or suspicious activity. Additionally, platforms maintain a unified audit trail by linking each verification result to the user’s history, simplifying reporting and compliance.
Generally, the benefits of identity and access management systems integrated with modern IDV platforms include:
Reducing AI-enabled fraud and impersonation: High-risk transactions or sensitive operations can trigger additional IDV checks for certain users based on their access level and risk profile. Biometric verification and step-up identity checks help reduce account takeover and impersonation risks. What’s more, IDV platforms that include modern security measures like deepfake and injection attack detection, robust liveness checks, border-level ID authentication, and cross-verification through government databases enhance companies’ protection against all types of synthetic identities and manipulated data.
Improving user trust without adding friction: IDV platforms offer advanced workflow customization. Administrators can configure branches, retries, and step-up rules to keep verification processes clear and proportionate to user risk. This reduces the likelihood of “over-verification,” where low-risk users face unnecessary checks.
Supporting global, remote-first operations: Scaling services to new markets becomes easier when IDV is integrated as part of the IAM architecture. Workflows, data storage, and access controls are managed centrally rather than distributed across application code, scripts, or isolated tools.
Keep user identity in focus with Regula
Managing numerous digital identities under IAM policies is anything but simple. Risk managers must ensure security across all identity and access processes while complying with fraud prevention, technical and KYC/AML requirements. At the same time, these processes must remain user-friendly to avoid increasing drop-off rates.
Adding an IDV layer to this system strengthens security without sacrificing user experience or operational efficiency.
Here is how the Regula IDV Platform supports this approach:
Ready-to-run white-label components for collecting and securely transmitting identity data to your systems.
Identity lifecycle management with flexible orchestration and customized workflows across every stage of the user journey.
A complete user database, including personal information and biometric data.
Comprehensive document and biometric verification, backed by the world’s largest document template database of 16,000+ items from 254 countries and territories.
Real-time facial recognition and liveness detection compliant with the ISO 30107-3 PAD standard to prevent the use of static images, printed photos, video replays, injection attacks, or masks.
Precise face matching and face identification to ensure the same person appears in different photos or to find a person by their image in an existing face database.
AML/PEP screening and validation against trusted global databases.
User data management and analytics to support continuous monitoring and compliance.
Seamless integration with your existing technology stack through flexible connectors.
Effortless adherence to regulations across multiple jurisdictions with robust, built-in compliance capabilities.
With identity verification embedded into IAM, organizations gain not only stronger protection, but also clearer oversight and long-term scalability.
Learn more about your opportunities with Regula!