A multinational bank, an online casino, and a crypto exchange encounter similar obstacles when implementing KYC into the company’s daily routine. Many of them pop up at the beginning of the user journey—at the identity verification stage.
Here are five key KYC challenges Regula customers—both global enterprises and local companies—face most, as well as their possible solutions.
We’ll deliver hand-picked content from Regula’s experts into your inbox
1. If your KYC involves demanding manual work
Paper-based KYC flow seems to be a common practice. This approach also appears to be more reliable for some companies, including financial institutions. However, low digital availability is becoming a critical problem for the industry. During the pandemic, 41% of European customers were unable to access financial services due to a lack of alternative online channels.
In addition to inconvenience for customers, an in-person ID verification process may also be less secure. An ordinary employee without a background in forensics can’t compete with machines in terms of the thoroughness of authenticity checks. They simply can’t read data encoded in a passport’s MRZ or validate an RFID chip on a biometric identity document with the naked eye.
Moreover, to comply with all KYC requirements, you need to collect customer information: their name, address, date of birth, and identification number, to name a few.
Manually entering these critical pieces of data is error-prone and time-consuming. It also slows down the whole ID verification process, and this is something customers don't appreciate.
How to fix: IDV automation with a complete set of authenticity checks
A human touch is a great thing, but not in the identity verification field. In the vast majority of cases, you can ensure that all the security boxes are checked with no human involvement. Implementing automated solutions accelerates the identity verification process and makes it more thorough and secure.
The authenticity checks provided by IDV software may include MRZ, barcode, and RFID chip reading and verification, as well as checking the presence of dynamic security features, such as holograms, and a set of cross-checks to make sure that it is a real passport or ID. All of these are difficult to capture when applying manual checks.
UBS, the largest private bank in the world, is a great example of how you can use KYC automation. For a customer, the identity verification process boils down to a few easy steps, like taking an ID photo and a selfie. Meanwhile, the IDV software behind the scenes conducts deep checks based on the document type.
By addressing KYC compliance challenges, the solution is customer-centric. All banking services are available to new customers 24/7 in just five minutes. Plus, all necessary data is entered into the systems automatically.
eKYC Explained: Why the Future Is Digital. Learn more
2. If you have a high false positive rate
Imagine your legitimate customer sees an alert after scanning their fully authentic ID to access your system. Due diligence is always a good path to follow, especially in regulated industries. However, errors resulting from imperfect algorithms can be a reputational risk for your company.
If your IDV solution flags trusted customers as bad actors, you also lose profits. According to J.P. Morgan, false positive losses account for 19% of the total cost of fraud, whereas actual fraud losses make up only approximately 7%.
Possible system errors may become more frequent when more foreign customers try to access your services. Regula’s global survey shows that four out of every five financial organizations have reported a surge in the number of verification cases involving non-resident IDs. This is related to the recent trend of increasing digital nomadism.
The fact is, many businesses have to verify foreign identity documents manually due to a lack of variety of ID templates that some automated systems can process. Manual document verification is a challenge in itself (see point 1), especially when your European employees have to verify a new document, say, an Ethiopian ID card, for the first time in their lives.
All of this complicates customer onboarding as a part of the KYC process, especially when avoiding false positives is crucial.
How to fix: Extensive document template database and technical know-how
There are no insignificant details in ID verification. For example, if your solution can’t distinguish between a Latin and Cyrillic “M,” a false positive may occur.
To be considered reliable, the machine-learning technology under the hood of the IDV solution should be informed by large datasets of authentic and tampered documents. By analyzing and comparing terabytes of data, AI and ML algorithms can detect patterns that help identify forged and legitimate documents provided during KYC procedures.
By mapping out a coherent KYC strategy, you can rely on identity verification solutions backed by years of experience and an in-house research and development team. This can give you confidence that the software is constantly improving, while all imperfections are fixed.
The extensive and regularly updated database an IDV vendor provides keeps your KYC systems relevant, since issuing authorities sometimes tweak minor details in identity documents, such as ink color. As a result, you may deal with different versions of the same passports—newer and older ones. Although both are legitimate, your IDV solution, with no recent references, can mistakenly flag newer versions as suspicious. This also helps identify obsolete blanks and patterns, since fraudsters often make forgeries using old document versions.
As a global developer of forensic devices and IDV solutions, Regula possesses the largest document template database in the world. It consists of over 16,000 items issued in 254 countries and territories, and continues to be replenished with new samples. This enables you to verify the identity documents of foreign customers as quickly as domestic IDs.
3. If you're trying to reduce fraud risks
Regula’s global survey revealed that every fourth bank reported experiencing over 100 identity fraud incidents in the past year. For 31% of banking organizations, the cost of such incidents was nearly half a million dollars and more.
However, by implementing KYC procedures, businesses can focus more on revealing grave problems like global money laundering, corruption, and terrorist financing schemes. As the lesser evil, identity fraud attempts may go unnoticed. Nevertheless, fake IDs are a constant component of criminal schemes. Moreover, this threat is widespread and costly.
With the arrival of digitalization, businesses increasingly face advanced identity fraud techniques. Intruders alter personal data in the visual zone and MRZ, modify photos and document patterns, and clone RFID chips.
If you have no dedicated software or devices to detect and prevent different types of identity fraud, your business stays unprotected.
How to fix: Identity fraud detection capabilities
Multi-factor authentication (MFA) is a must for banks and fintech companies. Many of them use facial recognition or fingerprints as an additional security layer. The IDV solution you use for this purpose can enhance your MFA flow by detecting any fraudulent alterations in the user's assets.
For example, Regula Face Reader SDK provides special tests for each selfie customers take during authentication to ensure that they are not spoofs or fakes, but live individuals. The AI-based liveness detection technology considers 45 biometric parameters when analyzing a portrait. The solution matches the selfie to the photo on the passport or ID, the RFID chip, and the customer's image in your database.
In addition, you have the option to upload images and link them to specific names. This allows the system to conduct searches in both directions—when you present a photo, it can search for the corresponding entry in the database, and vice versa. For instance, you can establish a group called "Fraudsters" and search for potential scammers within that group of risk people when needed.
4. If you're struggling to comply with regulations
There are a plethora of national, regional, and global KYC regulatory standards companies must take into account. What’s worse, they become more stringent every year. Plus, you never know if your current policies will be relevant in a couple of months.
Many governments now praise and support digitalization in many industries, including Banking. Example: In Europe, the basis for KYC is the EU AML Directives, which, among others, define possible IDV schemes. The corresponding eIDAS framework is developed as a regional standard. As expected, EU residents will increasingly use digital tokens provided by state electronic identification schemes like a Dutch DigiD for online transactions, which have the same legal status as traditional identity documents across the region. Since more people and businesses want to open bank accounts and use financial products digitally, a paperless future is possibly just around the corner.
However there is no uniformity; different countries employ diverse technologies, so their stages of digitalization vary, from in-person verification as a widespread practice, to full adoption of eIDs—electronic identification with a digital ID.
As a result, remote identity proofing laws, regulations, and practices may be more complicated at the national level. For instance, Germany, Italy, Luxembourg, and Portugal define video calls with an operator as a permissible online identity verification approach. Bulgaria, Estonia, Greece, and Norway claim to use a “selfie-id” or remote automatic systems. Some countries, like France or Spain, are willing to combine several ID verification methods in KYC.
Businesses targeting different regions have to stay compliant everywhere. This makes compliance with the law one of the most difficult KYC challenges to overcome.
How to fix: Primary compliant IDV vendors
Since the regulatory landscape is always changing, smoothly scalable and customizable solutions are a good option. That means you can easily keep them up to date to stay compliant with new requirements, both local and global.
There are some basic features you have to consider when looking for a long-term IDV partner. Cross-platform solutions enable you to make your services available to all users, including ones who prefer mobile devices. You can add another security layer to your systems by choosing vendors that adopt a “zero trust to mobile” approach in their software. This allows reverifying the RFID chip that biometric identity documents contain on the server side. Moreover, on-premise solutions make you more compliant, as you won’t have problems if more strict requirements for customer data processing appear.
Biometrics checks can also be a critical part of your IDV solution, since the biometric authentication component in the KYC flow is mandatory in many countries. For example, the Liechtenstein Due Diligence Act (DDA) requires local banks and fintech companies to use it.
Yet product performance metrics, such as accuracy rates, also matter. Ultimately, the KYC guidelines are grounded in best practices that consider not only the prevention of fraud but also the convenience for users.
5. If you want to improve customer experience
Mandatory in-person visits, long forms to fill out, and the inability to verify documents remotely are obstacles for many of your clients. Your KYC process should be compliant yet smooth. Otherwise, you may lose your customers.
Most industry participants recognize the significance of customer experience during the initial stages, particularly during the onboarding process. According to Regula’s global survey, 61% of finance-related businesses claim that customer experience improvement is one of the most significant success indicators of IDV solution deployment.
However, digitalization itself is not the whole solution. When you add an online ID verification component into your flow, it should complement the overall system.
How to fix: Customizable IDV solutions
You can choose from many solutions with UI customization features and default localization possibilities.
Applying automation at the time-consuming stages of ID verification, like document type detection and image capture, will help you deliver a handy and user-friendly solution.
The availability to integrate the IDV component into multiple platforms, from web to mobile, makes KYC procedures more convenient for your customers.
Regula provides you with comprehensive IDV technologies, including ones based on biometrics, that you can seamlessly incorporate into your systems. Importantly, identity verification stays compliant and frictionless.
Build a robust KYC system with a reliable partner
Along with new types of fraud, updated ID templates, and the latest global trends, IDV and KYC frameworks are also dynamically changing. Regularly reviewing and revising your KYC strategy is crucial for staying up to date with all the trends and demands.
However, first, you need a firm foundation. Below, take a look at the core components of a full-fledged IDV solution that meets all the main KYC challenges:
-
Automated data entry and authenticity checks under the hood
-
An extensive document template database and solid knowledge of ID verification nuances
-
Advanced fraud detection
-
Fully compliant with current KYC requirements applicable in regions and states where your services are present/offered
-
Application-specific customization and cross-platform availability
Regula Document Reader SDK and Regula Face SDK meet all these requirements. Here is how these IDV solutions can be implemented into your KYC scenario:
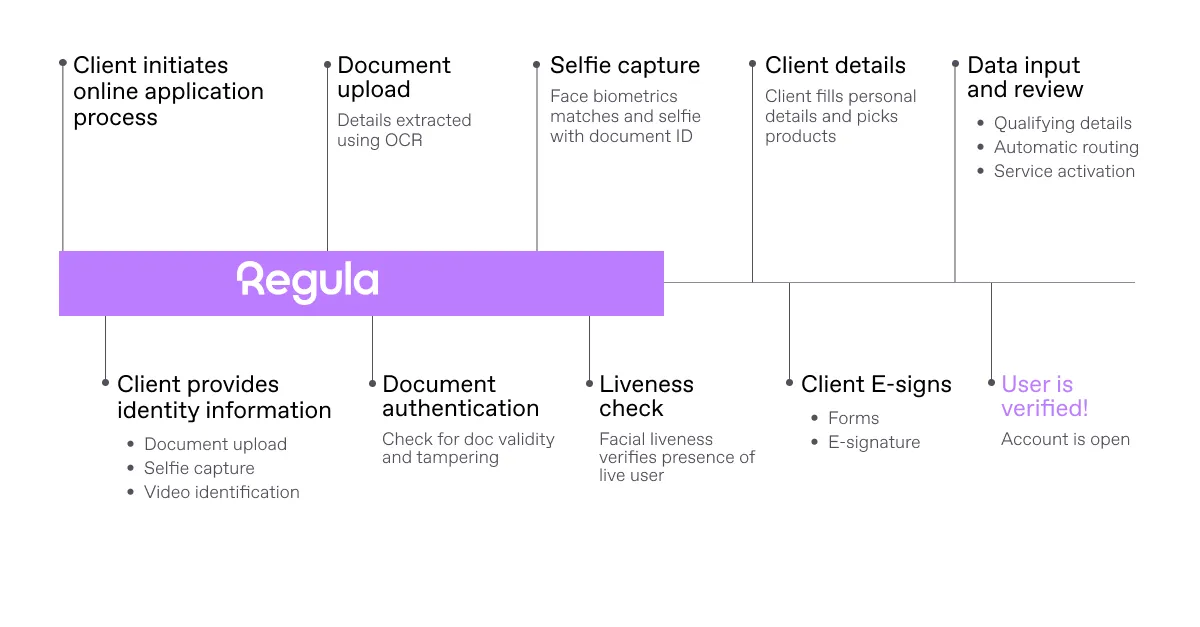
Regula solutions can be seamlessly integrated into your ID verification process to address critical KYC challenges


.webp)


.webp)
