KPMG’s 2025 banking survey reveals a clear tech shift in the industry.
Competitive pressure from fintechs and neobanks is driving investment in digital channels. In 2026, most surveyed banks plan to prioritize online banking (91%), mobile banking (93%), and digital wallets (91%).
At the same time, this shift requires major data modernization and upgraded IT infrastructure, including support for additional digital channels and third-party services. Legacy systems (81%), along with data privacy and risk concerns (93%), remain key blockers. They increase integration complexity and identity-related risks.
This makes digital identity orchestration as a centralized decision-making layer an urgent priority for banks during this transition.
In this article, we explore how this approach can be applied to identity lifecycle management, another critical component of modern digital-first financial institutions.
Get posts like this in your inbox with the bi-weekly Regula Blog Digest!
What orchestration means in banking and why it’s gaining traction
The term “orchestration” is often used broadly. In banking, it usually refers to the coordination of data and processes.
Data orchestration ensures that the right data gets to the right place at the right time under the proper governance and compliance rules. In practice, it means managing and coordinating data flows across systems, processes, and tools, covering stages such as collection, updates, and storage.
Example
A user registers in a mobile banking app. This typically involves entering personal details such as name, date of birth, phone number, and residential address. The data must then be verified, processed, and stored in line with internal and regulatory requirements.
Process orchestration coordinates end-to-end workflows, such as opening a bank account or adding a virtual debit card in an app. These workflows often involve multiple systems, teams, and third-party services.
Example
A registered user wants to open a bank account. This usually requires identity verification (IDV) through document and biometric checks, where the customer submits a government-issued ID and a selfie. To complete these checks, banks often rely on third-party software integrated into the workflow. The entire process must remain secure and compliant to ensure both verification accuracy and user privacy.
As a result, even a single operation, which may seem simple from the user’s perspective, consists of multiple “invisible” steps. This can be illustrated in the simplified diagram below.

Behind the scenes, all entered data and initiated transactions pass through multiple checkpoints, such as databases and internal servers. They are governed by various control layers, including identity and access management (IAM) tools, IDV solutions, credit bureaus, and other systems that form the bank’s IT infrastructure.
As the number of users and the volume of data grow, this network becomes increasingly complex. Orchestration helps simplify it by introducing a unifying mechanism that:
Integrates internal systems of record with specialized third-party services.
Embeds business policies such as risk thresholds and regulatory routing into customized workflows.
Enables real-time, event-driven decision-making rather than relying only on static compliance checks.
Why is identity verification a critical orchestration component for banks?
Historically, IDV in banking has been a legal requirement. Most global and local standards describing Know Your Customer (KYC) frameworks — for example, the US’ Customer Identification Program promotes a risk-based approach to IDV. This means low- and high-risk customer profiles must be handled differently.
Typically, KYC policies adopted by financial institutions include the following practices:
Customer Due Diligence (CDD) applies to low- and moderate-risk profiles. It includes standard identification procedures, during which essential customer information such as identity and address is collected and verified.
Enhanced Due Diligence (EDD) targets high-risk customers and transactions and requires deeper scrutiny. For example, beyond basic checks (ID document plus selfie), a bank may analyze a client’s source of wealth and source of funds. EDD may also include screening against watchlists and government databases, as well as checks for Politically Exposed Persons (PEP) or individuals from sanctioned jurisdictions.
Anti-money laundering (AML) measures combine KYC checks with transaction monitoring to detect links to activities such as money muling, illegal fund transfers, or trade-based money laundering.
Traditionally, these checks were conducted during in-person onboarding. With digitalization, however, banks must manage a growing number of identity-dependent interactions remotely. As online banks introduce or scale features such as digital wallets, investment products, and crypto or commodity trading, they face a recurring question: “Who is this person right now — and what level of risk control should apply?”
The online threat landscape adds another layer of complexity. In 2024, FinCEN reported increased suspicious activity involving deepfakes in fraud schemes, including the creation or alteration of fraudulent IDs to bypass IDV and authentication systems.
At the same time, synthetic identities, fueled by the wider access to AI tools, make presentation attacks harder to detect, especially for banks that lack layered controls such as:
Advanced ID document authentication that goes beyond basic visual inspection and data matching to include analysis of dynamic security features, electronic chips, and photo integrity.
Biometric verification with liveness detection to prevent AI-generated artifacts, video injections, screen replays, and similar attacks.
Ongoing monitoring of device and behavioral signals to flag suspicious transactions or unusual location patterns.
While robust IDV solutions may offer these controls individually, delivering them consistently at scale is difficult without orchestration. The need to assess customer risk — and sometimes reverify identity — arises at multiple points in the customer lifecycle. Critical moments include onboarding, account updates and recovery, limit increases, new payee creation, and approval of unusual transactions. Compliance requirements also evolve over time and may introduce additional checks for customers from specific regions or risk categories.
All this makes IDV in modern banking highly dependent on orchestration. These processes must rely on timely, relevant data and well-designed, customizable workflows that adapt to context and risk.
Core orchestration advantages for IDV and fraud prevention in banks
Orchestration helps digital banks balance security, conversion, cost, and compliance through risk-adaptive identity journeys.
Here are the key patterns to apply:
Risk-based verification
Instead of running every check upfront, banks can delay higher-cost steps, such as document verification or biometric analysis, until risk signals appear. This helps control costs while maintaining protection across the customer lifecycle.
In practice, low-risk users pass through basic checks, while higher-risk signals automatically trigger stronger verification in a consistent way.

Orchestration helps risk-based automation for routine banking processes, such as ID verification during account opening, based on customer risk profile.
Dependency management across identity, credit, and compliance
Orchestration ensures that workflow steps happen in the correct order. For example, IDV precedes credit risk scoring.
This sequence matters as weak identity proofing upstream can distort downstream decisions and increase false positives or false negatives. Clean, verified identity data improves the accuracy of credit scoring, AML checks, and fraud detection.
Vendor waterfalling and operational resilience
Orchestrated workflows can “waterfall” providers. If one data source fails or returns incomplete results, the system automatically routes the request to another provider. This reduces user drop-off and protects conversion rates.
It also lowers operational risk. Banks avoid single points of failure in critical IDV steps, especially during traffic spikes, service outages, or regional coverage gaps.
Real-time, event-driven monitoring
Traditional monitoring often runs on fixed schedules. Orchestrated workflows respond to events as they occur.
New risk signals, such as unusual behavior or device changes, can trigger step-up verification instantly. This shortens response times and reduces gaps caused by siloed systems or delayed data flows.
Auditability, traceability, and privacy-aware governance
Identity workflows process highly sensitive data: documents, biometrics, and personal information. Orchestration centralizes how this data is used, stored, and shared.
This improves traceability for AML and KYC compliance and reduces operational complexity by replacing fragmented point-to-point integrations.
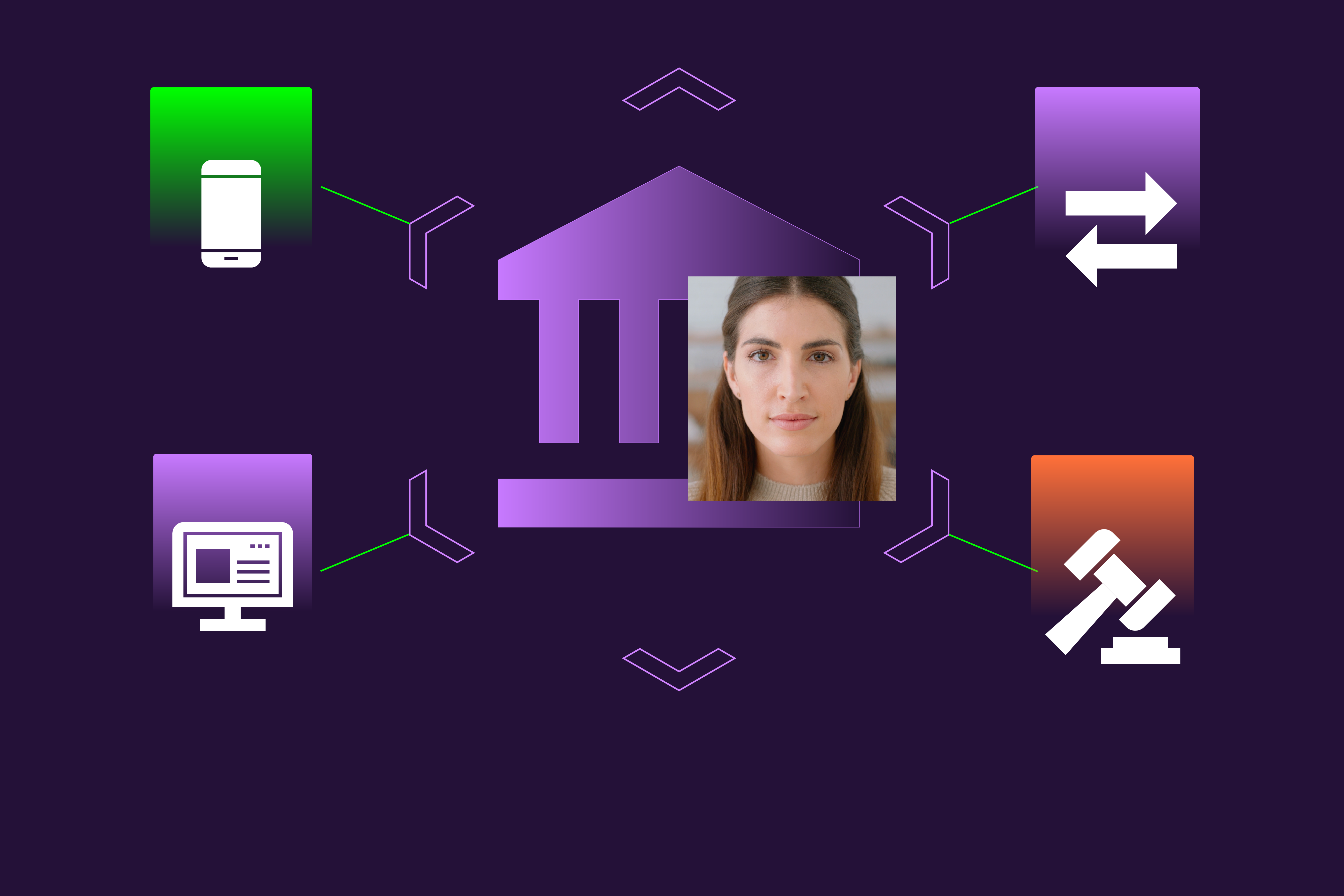
Cross-channel consistency
Banks operate across mobile apps, web platforms, branches, and partner ecosystems — and customers expect a consistent experience across all of them.
Orchestration connects identity signals across channels. As a result, customers are not treated as “new” each time they switch touchpoints, while fraud teams gain a unified risk view. This alignment strengthens both user experience and fraud control.
IDV platforms as an orchestration-ready solution
Orchestration turns identity signals into action across onboarding, payments, suspicious activity, and account changes.
To support this model, banks need a flexible service that orchestration engines can call at any point in the customer lifecycle — a role well suited to modern IDV platforms.
Unlike standalone IDV tools, platforms offer reusable proofing components — such as document authentication, biometric verification, and database checks — that can be configured based on risk level, region, product type, or channel. Instead of returning a simple pass/fail result, they provide structured decision signals. This allows banks to explain, audit, and justify every step-up action.
Strong privacy controls and configurable data-handling policies are equally important, especially as banks modernize under tighter regulatory and data protection requirements.
The Regula IDV Platform is built with this orchestration-first approach in mind. Learn more about its features and how it supports risk-based identity workflows.